The ask
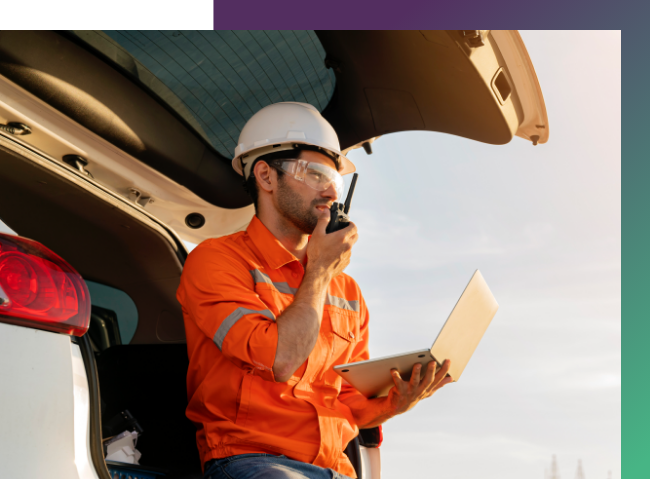
A security systems provider was looking to improve its ability to detect events around its geographical perimeters. Spanning kilometers of land and containing thousands of fibre sensors, the client was already using something called Distributed Acoustic Sensing (DAS) technology to trigger alarms whenever a perimeter breach occurred.
However, this DAS system could not determine whether a breach was caused by human or environmental forces – such as leaves, branches, animals, or weather conditions. Without this information, time and resources were often being spent investigating breaches that were not actual intrusions, and response to genuine breaches was being impeded.
The client was looking to introduce this capability, but had already significantly invested in DAS, which would be costly and disruptive to replace. They therefore needed a way to leverage this existing asset to drive new value and classify breaches with accuracy.

KEY OBJECTIVE: BE ABLE TO REMOTELY DISTINGUISH BETWEEN HUMAN AND ENVIRONMENTAL FORCES ENHANCING EXISTING DAS TECHNOLOGY.
What we did
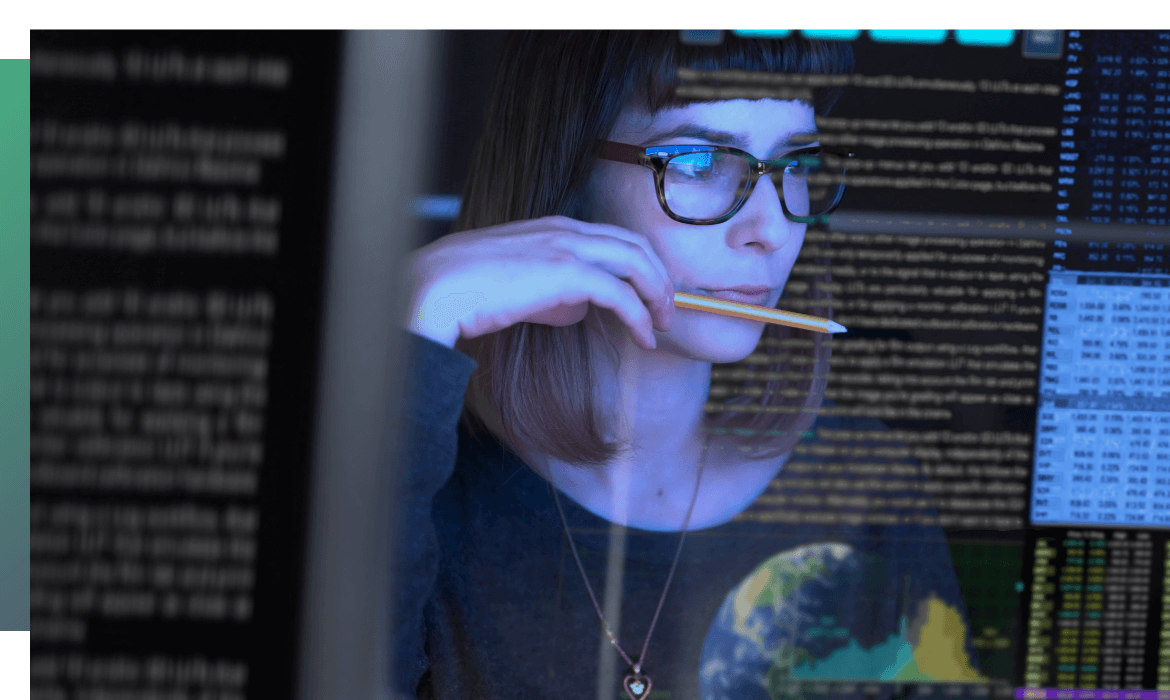
We decoded the historical data stored on the company’s sensors using Deep Learning algorithms to analyze their breaches. This helped us understand a range of intrusions based on several circumstances in different conditions. As a result, our technology is able to monitor a breach within 5 seconds and accurately trigger an alarm 98% of the time.
This means that the client spends less time and resources investigating false alerts. Due to the heightened level of accuracy, they’re able to use the technology in harsh or active environments without worrying about false breaches.
The process
Under a controlled context, we aggregated multiple historical data sources, and created a Deep Learning model to accurately predict, classify, and label breaches. We then applied data augmentation techniques to further train the algorithms and improve surveillance accuracy. Once all of the data from testing was gathered, we tested the solution in a real-life context and environment.
Result
5 SECONDS TO MONITOR BREACHES, WITH 98% ACCURACY OF ALARM TRIGGERS.
By the completion of the project, the client had an A.I. enabled process automation solution capable of making accurate predictions and lowering risk. This enabled real intrusions to be acted upon more quickly and appropriately, while saving time and resources on investigating natural breaches.
Are you working on something similar?
Get in touch and we’d look to discuss how we can help you.


